Spread Spectrum Techniques
Spread-Spectrum techniques are methods by which a signal (e.g. an electrical, electromagnetic, or acoustic signal) generated with a particular bandwidth is deliberately spread in the frequency domain, resulting in a signal with a wider bandwidth.
These techniques are used for a variety of reasons, including the establishment of secure communications, increasing resistance to natural interference, noise and jamming, to prevent detection, and to limit power flux density (e.g. in satellite downlinks).
Spread spectrum is designed to be used in wireless applications (LANs and WANs). In wireless applications, all stations use air (or a vacuum) as the medium for communication. Stations must be able to share this medium without interception by an eavesdropper and without being subject to jamming from a malicious intruder.
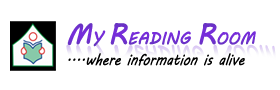
To achieve these goals, spread spectrum techniques add redundancy, they spread the original spectrum needed for each station. If the required bandwidth for each station is B, spread spectrum expands it to Bss such that Bss >> B. The expanded bandwidth allows the source to wrap its message in a protective envelope for a more secure transmission.
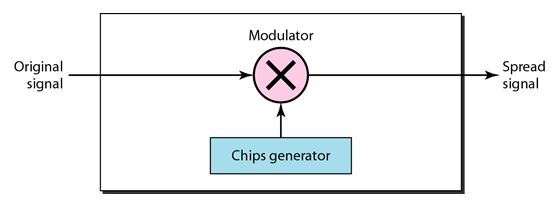
The following figure shows the idea of spread spectrum. Spread spectrum achieves its goals through two principles:
1. The bandwidth allocated to each station needs to be, by far, larger than what is needed. This allows redundancy.
2. The expanding of the original bandwidth B to the bandwidth Bss must be done by a process that is independent of the original signal. In other words, the spreading process occurs after the signal is created by the source.
After the signal is created by the source, the spreading process uses a spreading code and spreads the bandwidth. The figure shows the original bandwidth B and the spreaded bandwidth Bss. The spreading code is a series of numbers that look random, but are actually a pattern.
There are two techniques to spread the bandwidth:
Frequency Hopping Spread Spectrum (FHSS)
Direct Sequence Spread Spectrum (DSSS).
1. Frequency Hopping Spread Spectrum (FHSS):
The Frequency Hopping Spread Spectrum (FHSS) technique uses M different carrier frequencies that are modulated by the source signal. At one moment, the signal modulates one carrier frequency; at the next moment, the signal modulates another carrier frequency. Although the modulation is done using one carrier frequency at a time, M frequencies are used in the long run. The bandwidth occupied by a source after spreading is BpHSS >> B.
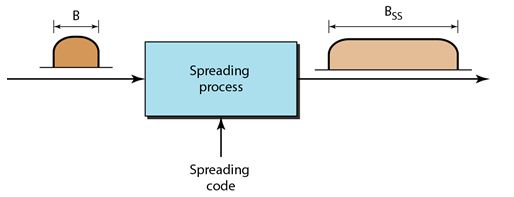
The following figure shows the general layout for FHSS. A pseudorandom code generator, called pseudorandom noise (PN), creates a k-bit pattern for every hopping period Th•
The frequency table uses the pattern to find the frequency to be used for this hopping period and passes it to the frequency synthesizer. The frequency synthesizer creates a carrier signal of that frequency, and the source signal modulates the carrier signal.
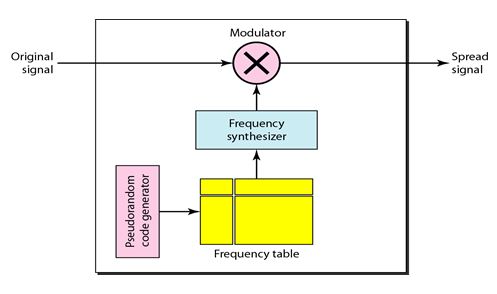
For Example M is 8 and k is 3. The pseudorandom code generator will create eight different 3-bit patterns. These are mapped to eight different frequencies in the frequency table as shown in the following figure.
The pattern for this station is 101, 111, 001, 000, 010, all, 100. Note that the pattern is pseudorandom it is repeated after eight hoppings. This means that at hopping period 1, the pattern is 101. The frequency selected is 700 kHz, the source signal modulates this carrier frequency.
The second k-bit pattern selected is 111, which selects the 900-kHz carrier; the eighth pattern is 100, the frequency is 600 kHz. After eight hoppings, the pattern repeats, starting from 101 again.
If there are many k-bit patterns and the hopping period is short, a sender and receiver can have privacy. If an intruder tries to intercept the transmitted signal, she can only access a small piece of data because she does not know the spreading sequence to quickly adapt herself to the next hop. The scheme has also an anti-jamming effect. A malicious sender may be able to send noise to jam the signal for one hopping period (randomly), but not for the whole period.
Bandwidth Sharing
If the number of hopping frequencies is M, we can multiplex M channels into one by using the same Bss bandwidth. This is possible because a station uses just one frequency in each hopping period; M - 1 other frequencies can be used by other M - 1 stations. In other words, M different stations can use the same Bss if an appropriate modulation technique such as multiple FSK (MFSK) is used.
2. Direct Sequence Spread Spectrum
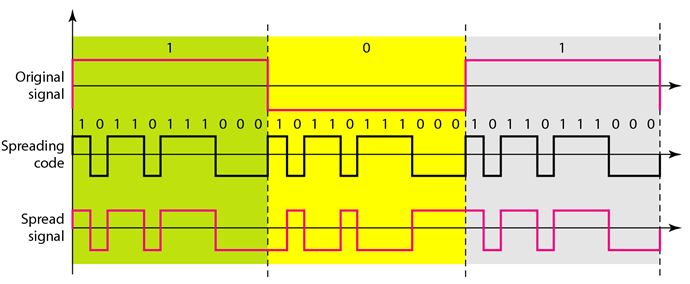
The direct sequence spread spectrum (nSSS) technique also expands the bandwidth of the original signal, but the process is different. In DSSS, we replace each data bit with n bits using a spreading code. In other words, each bit is assigned a code of n bits, called chips, where the chip rate is n times that of the data bit. The following figure shows the concept of DSSS.
As an example, let us consider the sequence used in a wireless LAN, the famous Barker sequence where n is 11. We assume that the original signal and the chips in the chip generator use polar NRZ encoding. The following figure shows the chips and the result of multiplying the original data by the chips to get the spread signal.
In the figure, the spreading code is 11 chips having the pattern 10110111000 (in this case). If the original signal rate is N, the rate of the spread signal is 11N. This means that the required bandwidth for the spread signal is 11 times larger than the bandwidth of the original signal. The spread signal can provide privacy if the intruder does not know the code. It can also provide immunity against interference if each station uses a different code.
You May Also Like:
Multiplexing and Types of Multiplexing
Frequency Division Multiplexing
Wavelength-Division Multiplexing
Time-Division Multiplexing
Back to DCN Questions and Answers